Phishing Emails at Work: How to Spot Fakes from Coworkers and Management
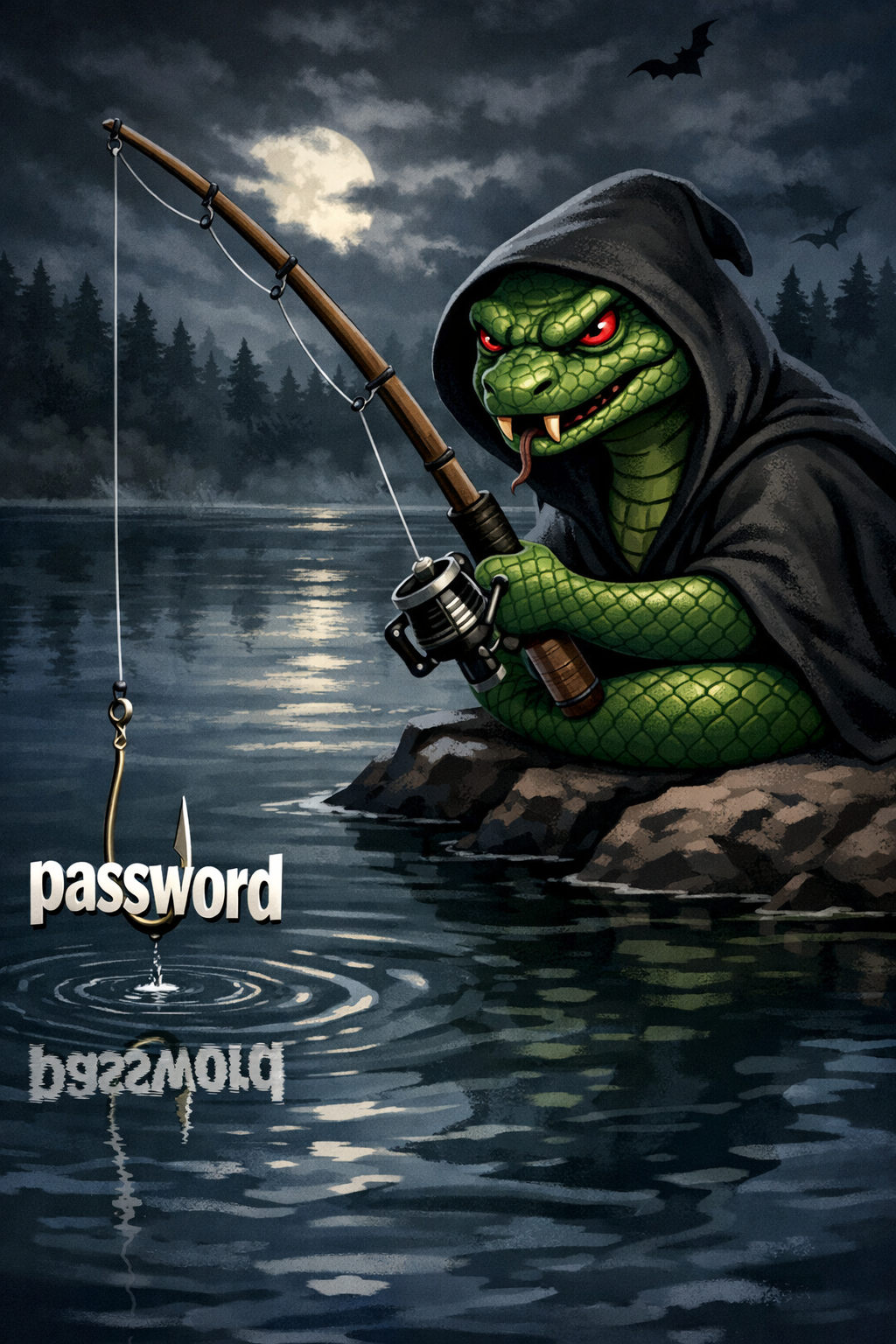
Phishing isn’t just the Nigerian prince emails from 2004. The modern version lands in your work inbox, looks like it came from your boss, and says something like “I need you to process this wire transfer before end of day” or “HR needs you to verify your direct deposit info — click here.” It works because it looks normal. It feels routine. And that’s the point.
How workplace phishing works
An attacker sends an email that appears to come from someone inside your organization — a manager, a coworker, someone in HR or finance. The email address might be spoofed to match exactly, or it might be one character off. The message asks you to do something: click a link, open an attachment, send sensitive information, or transfer money.
The requests are designed to feel urgent and plausible. A “CEO” asking an accounts payable employee to wire funds to a vendor. An “IT department” email saying your password expires today. A “coworker” sharing a document that requires you to log in to view it. These aren’t random — attackers research your company’s structure, learn names and titles from LinkedIn, and craft messages that fit the context.
This is called business email compromise, and the FBI’s Internet Crime Complaint Center consistently ranks it as one of the most financially damaging forms of cybercrime. It costs businesses billions every year.
Red flags in the email itself
The sender address is slightly off. Your CFO’s email is jsmith@yourcompany.com but this one came from jsmith@yourcompany.co or jsmith@yourcompamy.com. One letter. Easy to miss if you’re not looking.
The tone or dialect doesn’t match. This one is underrated. If your manager normally writes in casual, short sentences and you receive a message from them that’s suddenly formal, wordy, or uses phrasing they’d never use — pay attention. The same applies in reverse. People have consistent writing habits. If something reads like a different person wrote it, there’s a real chance a different person did. Trust that instinct.
It creates urgency. “This needs to happen before end of day.” “Don’t discuss this with anyone yet.” “I’m in a meeting and can’t talk — just handle it.” Pressure to act fast and skip verification is the oldest trick in the book.
It asks you to bypass normal procedures. Any email asking you to skip an approval step, use a new account number, or send information through an unusual channel should be verified through a separate communication method before you act on it.
The link doesn’t go where it claims. Hover over any link before clicking. If the display text says “yourcompany.sharepoint.com” but the actual URL points somewhere else, don’t click it.
Unexpected attachments. An invoice you weren’t expecting. A “voicemail” as a .zip file. A spreadsheet from someone who’s never sent you one. These are common delivery mechanisms for malware.
What to do when something looks suspicious
Don’t reply to the email. If you think a message from your boss might be fake, don’t hit reply to ask them — if the email is spoofed or the account is compromised, the attacker is the one who’ll respond. Instead, contact the person through a different channel. Call them. Walk to their desk. Send a separate message to the email address or phone number you already have — not the one in the suspicious message.
Don’t click anything. Don’t open attachments. Don’t click links. Don’t enable macros. If you already did, disconnect from the network and report it immediately.
Report it. If your company has an IT team, forward the email to them. If you don’t have an IT team — which is the reality for most small businesses — report it to whoever manages your systems, even if that’s the owner. The faster a phishing email gets flagged, the less damage it does.
Advice for small businesses without an IT department
Most phishing guidance assumes you have a security operations center or at least a dedicated IT person. Many small businesses have neither. The owner is the IT department, the security team, and the help desk. That doesn’t change the threat level — it just means you have to be more deliberate.
Train everyone, even if it’s informal. Sit down with your employees and talk about what phishing looks like. Show them examples. Make it clear that nobody will get in trouble for pausing to verify a request, even if it turns out to be legitimate. The cost of a five-minute delay to confirm a wire transfer is zero. The cost of sending $40,000 to a scammer is not.
Establish a verification rule for money and sensitive data. Any request involving money transfers, changes to payment information, W-2s, or personal employee data must be confirmed by phone call or in person. No exceptions. If someone emails asking to change their direct deposit account, you call them at the number you already have on file and confirm it. This single policy stops the majority of business email compromise attacks.
Use multi-factor authentication on everything. Email accounts, banking, payroll systems, cloud storage — all of it. If an attacker gets a password through a phishing link, MFA is what stops them from getting in. Most cloud services offer it for free. Turn it on.
Know who to call. Identify in advance who you’ll contact if something goes wrong. Your email provider, your bank, your insurance company, your attorney. Have those numbers somewhere accessible that isn’t your email, because your email might be what’s compromised.
What the law requires after a data breach
If your business suffers a breach — whether through phishing, malware, or any other method — and personal information is exposed, you don’t get to decide quietly that it’s not a big deal. Every U.S. state has data breach notification laws, and they apply to businesses of all sizes.
You must notify affected individuals. If personal information like Social Security numbers, financial account data, driver’s license numbers, or medical records is compromised, you are legally required to notify the people affected. The timeline varies by state, but many require notification within 30 to 60 days of discovering the breach. Some states, like Florida, require it within 30 days. Others give you more time, but none give you the option to stay silent.
You may need to notify your state attorney general. Many states require businesses to report breaches to the attorney general’s office, especially when the breach affects a certain number of residents. The thresholds and requirements differ by state.
You may need to notify credit reporting agencies. If the breach affects a large number of people (commonly 500 or more, depending on the state), you may be required to notify the major credit bureaus.
There are federal requirements in certain industries. If you handle health information, HIPAA has its own breach notification rules. Financial institutions are covered by the Gramm-Leach-Bliley Act. If you’re not sure which regulations apply to you, that’s something to sort out before a breach happens, not during one.
Failure to comply has consequences. State attorneys general can and do fine businesses for failing to notify after a breach. In some states, affected individuals can also pursue private legal action. Small businesses are not exempt from these requirements.
The practical step here is simple: find out what your state requires now. The National Conference of State Legislatures maintains a list of data breach notification laws by state. Know what applies to you before you need it.
The bottom line
Phishing works because it exploits trust and routine. An email that looks like it’s from your boss, asking for something that seems reasonable, during a busy workday — that’s a hard thing to question. But questioning it is exactly what stops these attacks.
Verify before you act. Use a second channel. Don’t let urgency override judgment. And if you run a small business, build these habits into your operations now — because the legal and financial consequences of a successful phishing attack don’t scale down just because your company is small.